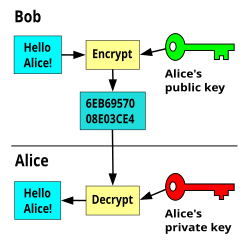
Private Key and public key are a part of encryption that encodes the information. Windows 7 and 8 key generator. Both keys work in two encryption systems called symmetric and asymmetric. Symmetric encryption (private-key encryption or secret-key encryption) utilize the same key for encryption and decryption. Asymmetric encryption utilizes a pair of keys like public and private key for better security where a message sender encrypts the message with the public key and the receiver decrypts it with his/her private key.
- Generating A Hash Code From Public And Private Keys Florida
- Generating A Hash Code From Public And Private Keys Are The Same In A Public Key Encryption Scheme
Mar 28, 2019 These keys are generated in pairs, consisting of a public key and a private key. The public key can be thought of as being an individual’s bank account, whilst the private key is the secret PIN to that bank account. The public key is cryptographically connected to a cryptocurrency address in the sense that the address is a representation of the public key.
Public and Private key pair helps to encrypt information that ensures data is protected during transmission.
Generating A Hash Code From Public And Private Keys Florida
Public Key
Public key uses asymmetric algorithms that convert messages into an unreadable format. A person who has a public key can encrypt the message intended for a specific receiver. The receiver with the private key can only decode the message, which is encrypted by the public key. The key is available via the public accessible directory.
Private Key
Generating A Hash Code From Public And Private Keys Are The Same In A Public Key Encryption Scheme
The private key is a secret key that is used to decrypt the message and the party knows it that exchange message. In the traditional method, a secret key is shared within communicators to enable encryption and decryption the message, but if the key is lost, the system becomes void. To avoid this weakness, PKI (public key infrastructure) came into force where a public key is used along with the private key. PKI enables internet users to exchange information in a secure way with the use of a public and private key.
Key Size and Algorithms
There are RSA, DSA, ECC (Elliptic Curve Cryptography) algorithms that are used to create a public and private key in public key cryptography (Asymmetric encryption). Due to security reason, the latest CA/Browser forum and IST advises to use 2048-bit RSA key. The key size (bit-length) of a public and private key pair decides how easily the key can be exploited with a brute force attack. The more computing power increases, it requires more strong keys to secure transmitting data.